Protecting Virtual Event Streams from Unauthorized Access

Protecting Virtual Event Streams from Unauthorized Access
As virtual and hybrid events become essential channels for business communication, securing event streams is critical for protecting content, revenue, and attendee trust. Risks such as unauthorized entry, content piracy, and link sharing can undermine event value and damage brand credibility. Modern event platforms must adopt layered security approaches to ensure that only authenticated participants can access and engage with live and on-demand sessions.
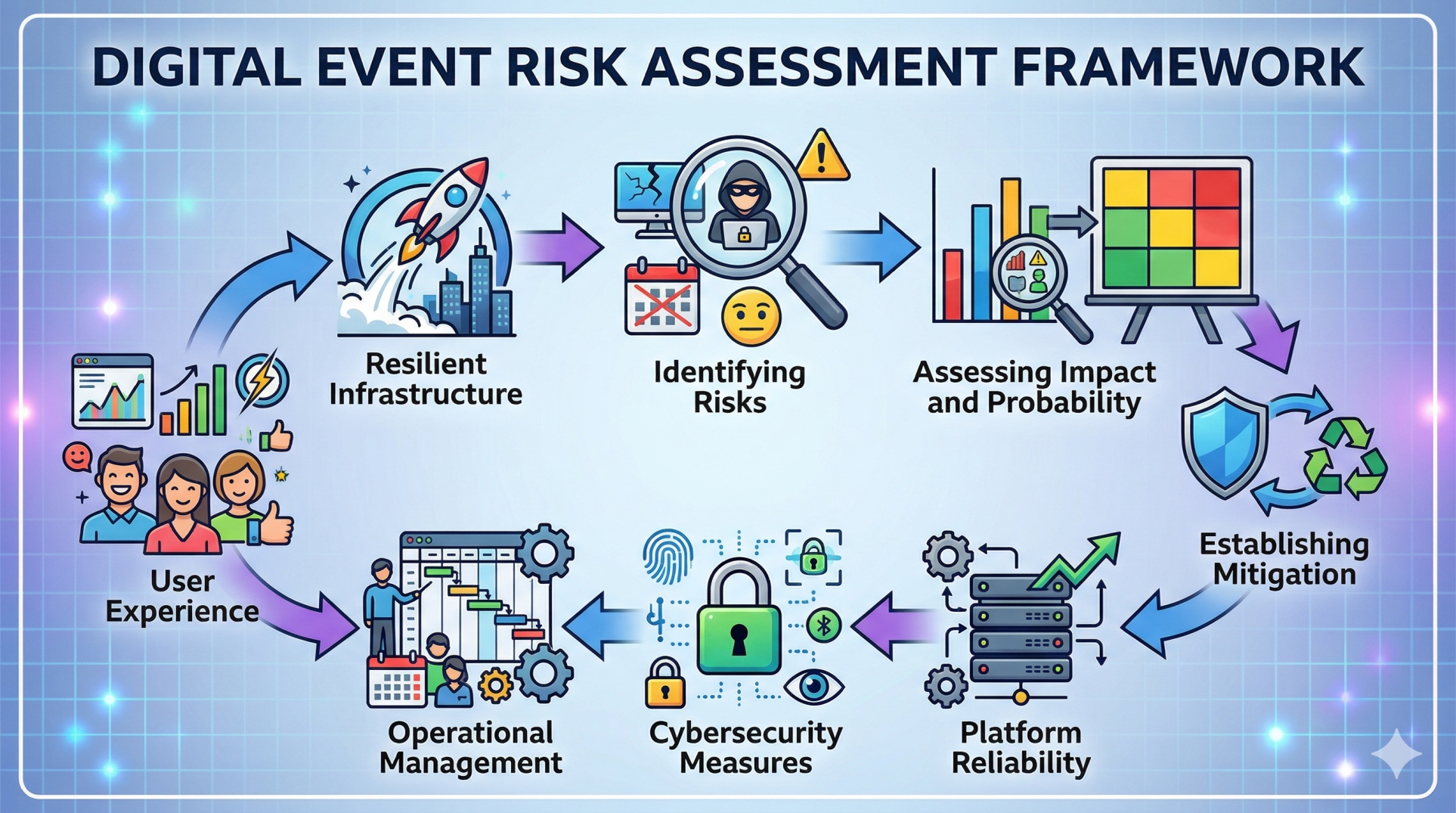
Step 1: Understanding the Risks of Unauthorized Access ⚠️
• Shared or exposed access links can allow unintended participants to join 🔗
• Screen recording and capture tools can enable content piracy 🎥
• Credential sharing can bypass access restrictions 🔑
• Unauthorized distribution reduces the value of paid events 💸
• Security gaps can harm brand reputation and compliance 📉
Step 2: Secure Authentication and Access Control 🔐
• Require verified user authentication through secure login systems 👤
• Implement single sign-on and multi-factor authentication for added protection 🔑
• Assign role-based permissions for attendees, speakers, and administrators 🧑💼
• Restrict access based on registration status and ticket level 🎫
• Limit concurrent sessions per user to prevent account sharing 🚫
Step 3: Tokenization and Session-Based Access 🎟️
• Generate unique, time-bound tokens for each session ⏱️
• Link tokens to specific users and devices 📱
• Prevent reuse of session links across multiple participants 🚫
• Automatically expire tokens after session completion ⌛
• Reduce risks associated with link sharing and unauthorized access 🔒
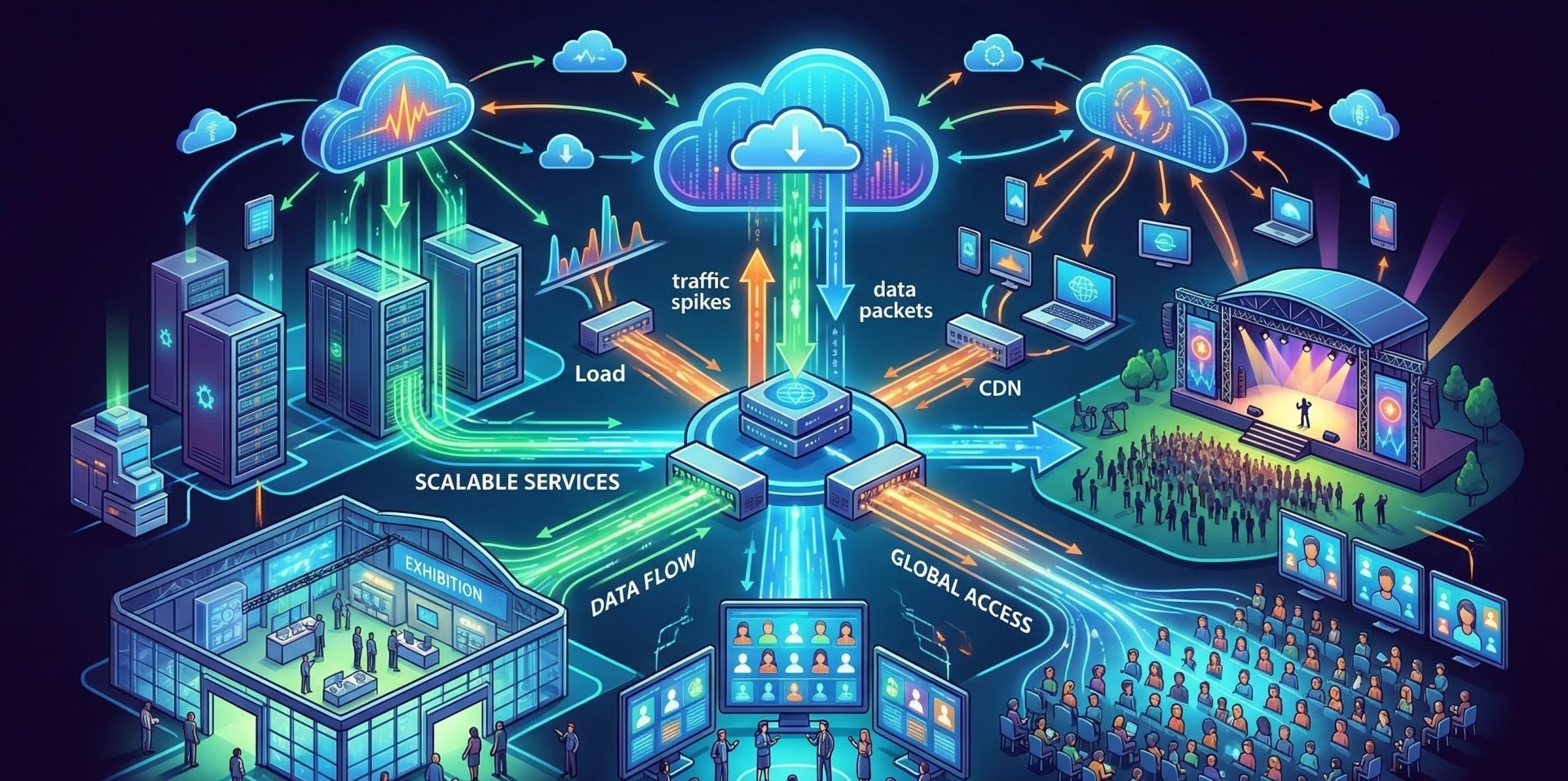
Step 4: Stream Encryption and Secure Delivery 🔒
• Encrypt video streams using established security protocols 🔐
• Deliver content through secure channels such as HTTPS 🌐
• Protect data during transmission across networks 📡
• Prevent interception and unauthorized playback 🚫
• Ensure compatibility with secure playback environments 💻
Step 5: Digital Rights Management (DRM) and Content Protection 🛡️
• Apply DRM technologies to control how content is accessed and used 📜
• Restrict downloading, copying, and redistribution of streams 🚫
• Block playback on unauthorized devices or platforms 📵
• Enforce viewing policies for premium or sensitive sessions 🎯
• Safeguard intellectual property and monetized content 💼
Step 6: Monitoring and Real-Time Threat Detection 👀
• Continuously track user activity and session behavior 📊
• Identify suspicious patterns such as multiple or unusual logins ⚠️
• Detect attempts to access restricted or protected sessions 🚫
• Trigger alerts for potential security incidents 🚨
• Enable rapid response to minimize impact and risk ⚡
Step 7: Watermarking and Content Traceability 🧾
• Embed visible or invisible watermarks into video streams 🎥
• Associate watermarks with individual users or sessions 👤
• Trace leaked or pirated content back to its source 🔍
• Discourage unauthorized recording or distribution 🚫
• Strengthen accountability across all participants 📌
Step 8: Key Security Priorities for Event Platforms 🎯
• Enforce strong authentication and access management 🔐
• Secure streams through encryption and protected delivery 🔒
• Prevent piracy using DRM and watermarking technologies 🛡️
• Monitor user activity for real-time threat detection 👀
• Maintain strict control over session access and sharing 🚫
Step 9: Compliance and Data Protection 📜
• Adhere to data privacy and protection regulations ⚖️
• Safeguard attendee identity and access credentials 🔑
• Ensure secure storage of user and session information 🗂️
• Maintain audit logs for compliance verification 📊
• Align security practices with enterprise standards 🏢
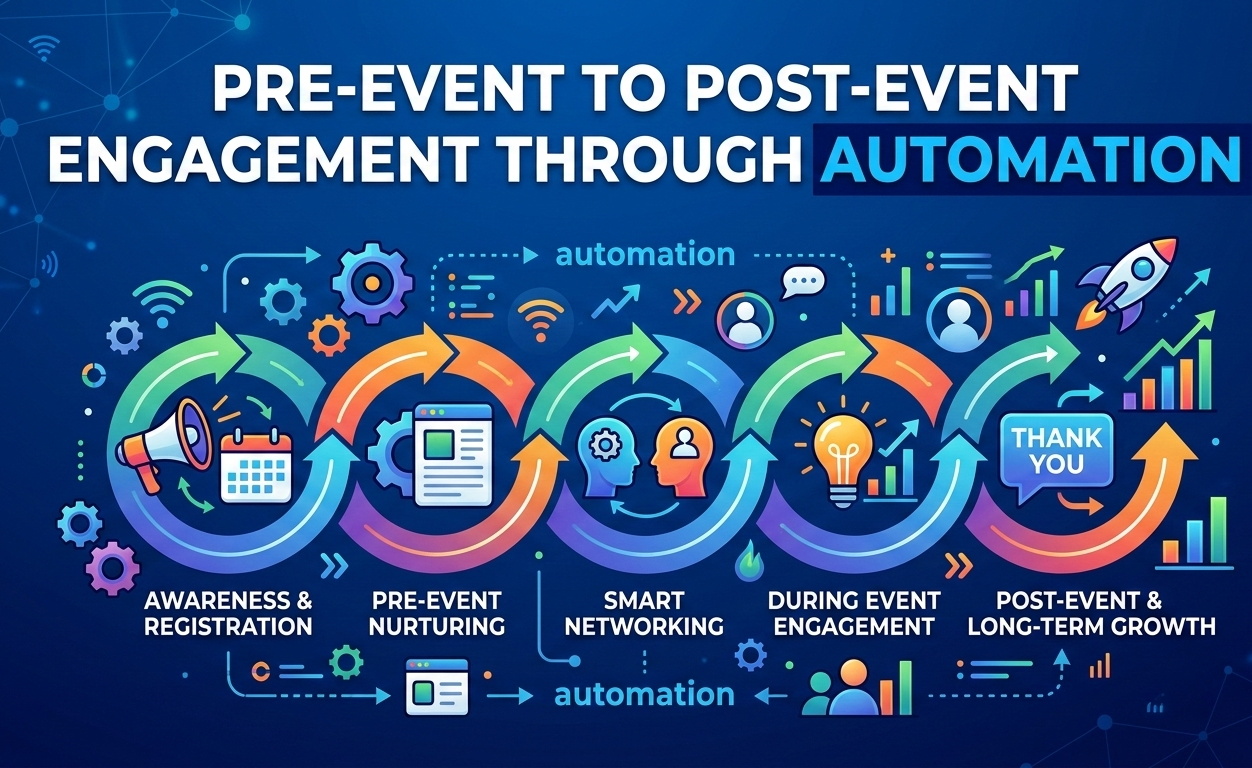
Step 10: Building Trust Through Secure Experiences 🤝
• Create a safe and controlled environment for all participants 🛡️
• Protect premium content and sponsor investments 💰
• Strengthen brand credibility through strong security practices 🏆
• Encourage engagement without concerns about misuse 😊
• Deliver reliable and secure event experiences consistently 🔄
Conclusion
Securing virtual event streams requires a comprehensive strategy that integrates authentication, encryption, monitoring, and content protection. By implementing layered security measures, event platforms can prevent unauthorized access, protect valuable content, and build trust with attendees and stakeholders. As digital events continue to expand, strong security practices will remain essential for delivering reliable and high-quality experiences.
See more blogs
You can all the articles below
Ready to Find Your Perfect Solution?
Let us show you how Event Software can transform your events