Secure Identity Verification in Event Technology

Secure Identity Verification in Event Technology
As event technology evolves, ensuring secure and seamless identity verification has become a critical priority. From large-scale conferences to exclusive corporate gatherings, verifying attendee identity is essential for maintaining security, preventing fraud, and delivering personalized experiences. Modern event platforms are moving beyond manual checks toward intelligent, automated verification systems that enhance both safety and user experience.
Step 1: Understanding Identity Verification Needs 🔐
• Identify different attendee types such as guests, staff, vendors, and VIPs 🎫
• Define access levels based on roles and permissions 🧩
• Determine verification requirements for physical and virtual events 🌐
• Balance security measures with attendee convenience ⚖️
• Establish clear identity validation workflows 📋
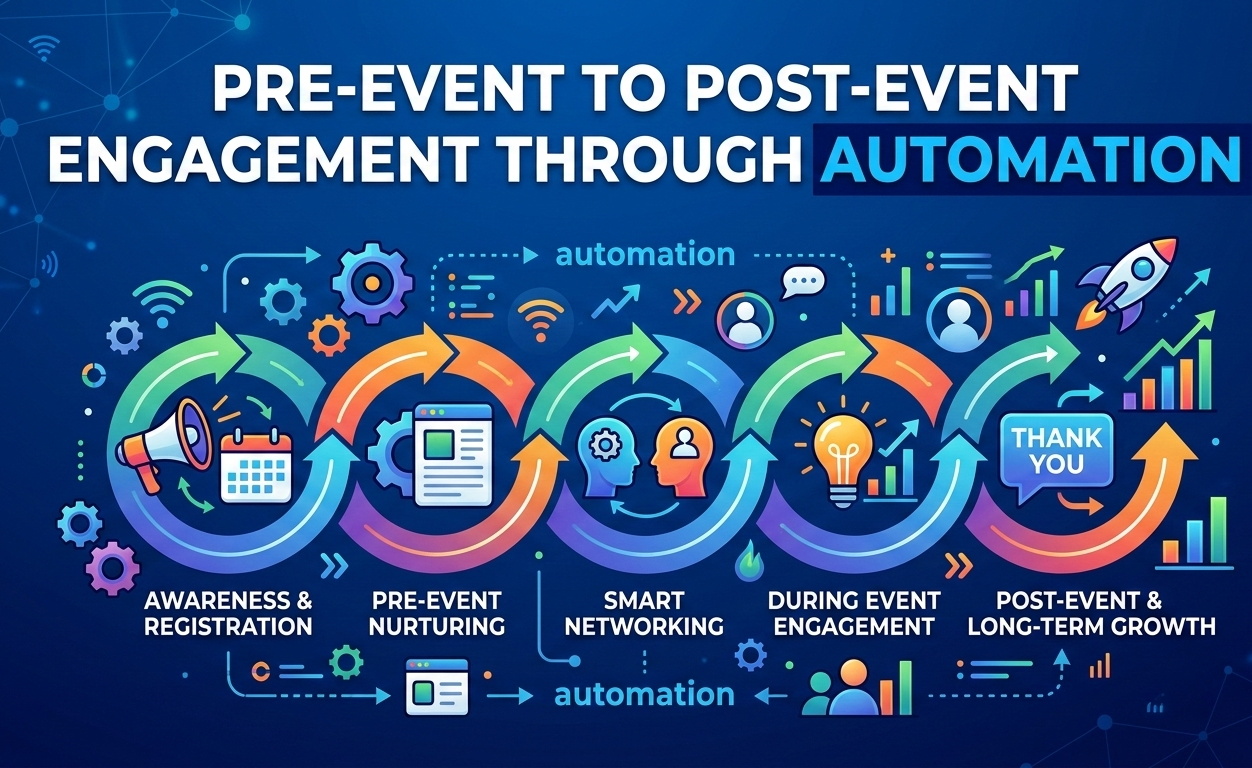
Step 2: Implementing Digital Registration and Credentialing 🪪
• Use secure online registration systems with verified user inputs 💻
• Generate unique digital credentials such as QR codes or badges 📱
• Enable pre-event identity validation to reduce on-site delays ⏱️
• Prevent duplicate or fraudulent registrations 🚫
• Integrate registration with identity verification systems 🔗
Step 3: Biometric and Multi-Factor Authentication 👁️
• Use biometric methods such as facial recognition or fingerprint scanning 🧬
• Implement multi-factor authentication (MFA) for sensitive access 🔑
• Combine physical and digital verification layers for higher security 🛡️
• Reduce reliance on easily shareable credentials 🚷
• Ensure fast and accurate identity validation at entry points ⚡
Step 4: Secure Access Control Systems 🚪
• Deploy smart access control points at entry and restricted zones 🚪
• Validate credentials in real time during check-in 🎟️
• Control movement within the venue based on permissions 🧭
• Monitor entry and exit activity for security tracking 📊
• Integrate with badge scanning and mobile authentication 📲
Step 5: Data Privacy and Compliance 🔒
• Protect attendee data with encryption and secure storage 🔐
• Comply with global data privacy regulations such as GDPR 📜
• Limit data collection to necessary information only ⚖️
• Provide transparency on how attendee data is used 👁️
• Implement secure data access and retention policies 🗄️
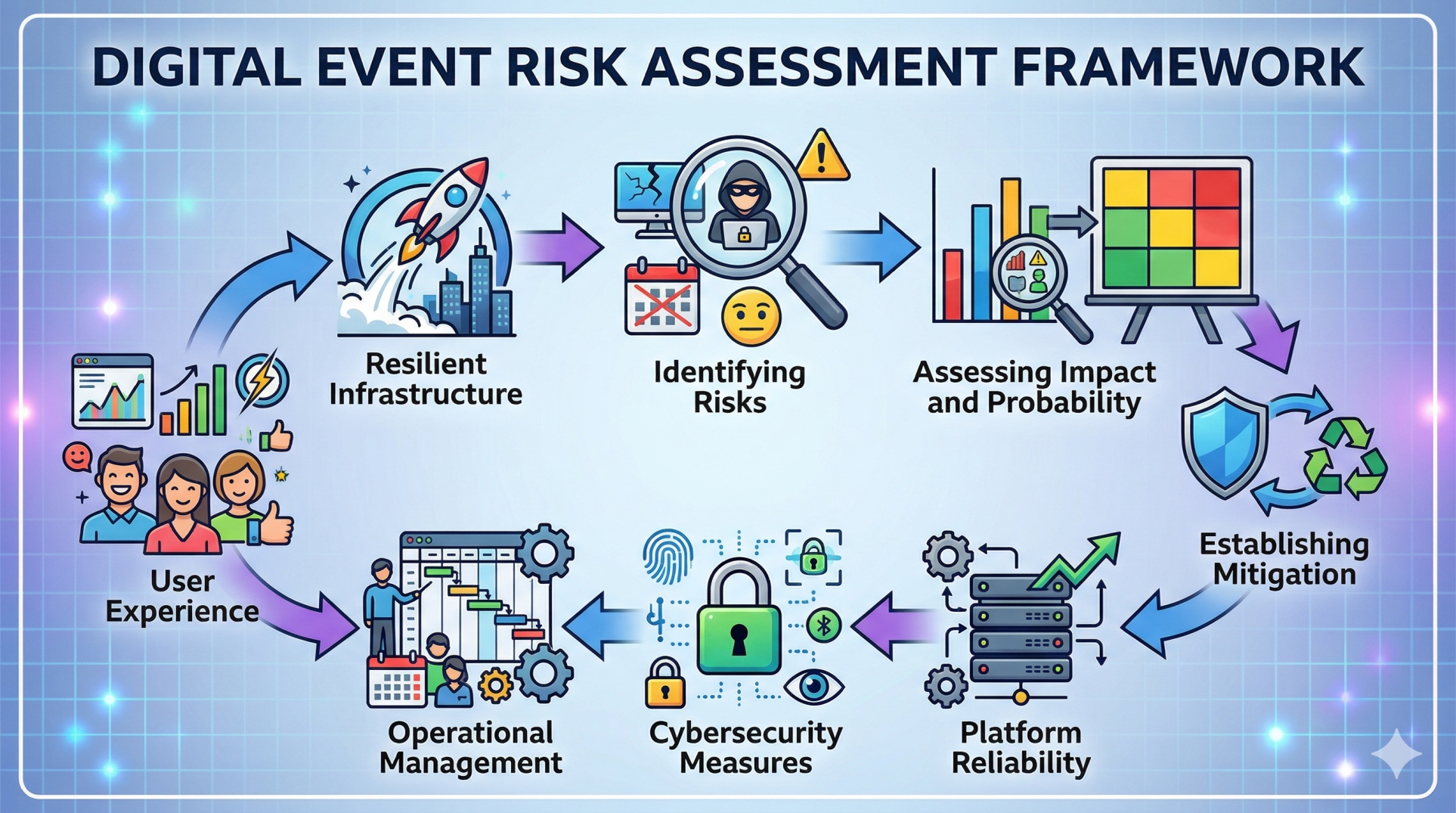
Step 6: Real-Time Monitoring and Threat Detection 📡
• Monitor attendee activity and access patterns in real time 📡
• Detect anomalies such as unauthorized access attempts 🚨
• Use AI-driven systems to identify potential security risks 🤖
• Enable instant alerts and response mechanisms ⚠️
• Maintain continuous visibility across the event environment 👀
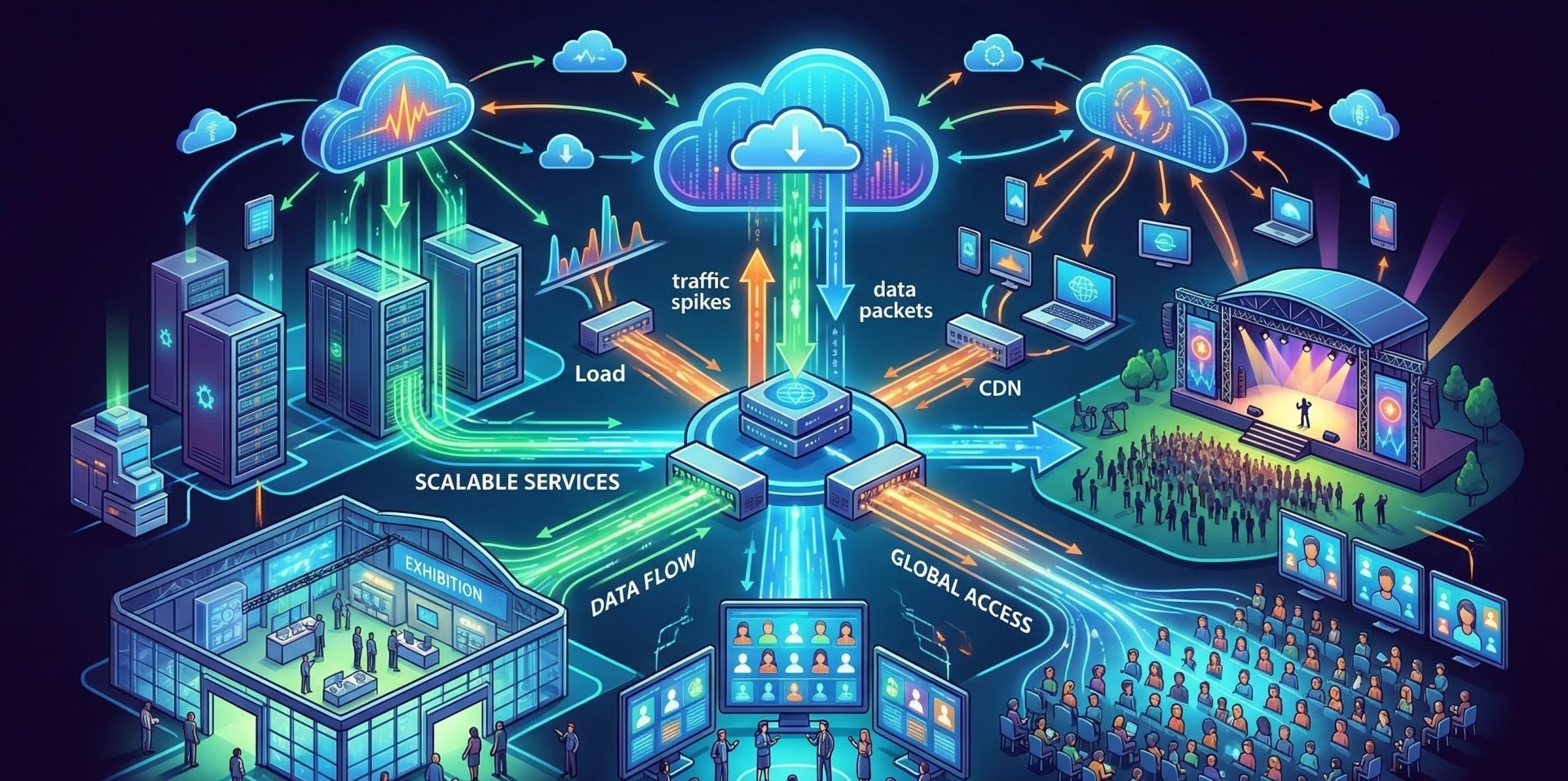
Step 7: Integration with Event Ecosystem 🔗
• Integrate identity verification with ticketing and event apps 🎟️
• Connect systems with venue security and management platforms 🏢
• Enable seamless data flow across all event technologies 🔄
• Ensure interoperability between verification tools and event software 🧠
• Support hybrid and virtual event identity validation 🌐
Step 8: Key Security Priorities 🛡️
• Accurate and reliable identity verification systems ✔️
• Seamless attendee experience with minimal friction ⚡
• Strong data protection and privacy compliance 🔒
• Scalable solutions for events of all sizes 📈
Step 9: Handling Exceptions and Fraud Prevention 🚫
• Detect duplicate or suspicious registrations early 🔍
• Prevent credential sharing and unauthorized access 🚷
• Establish manual override processes for edge cases 🛠️
• Train staff to handle identity verification issues effectively 👥
• Maintain logs for audit and investigation purposes 📑
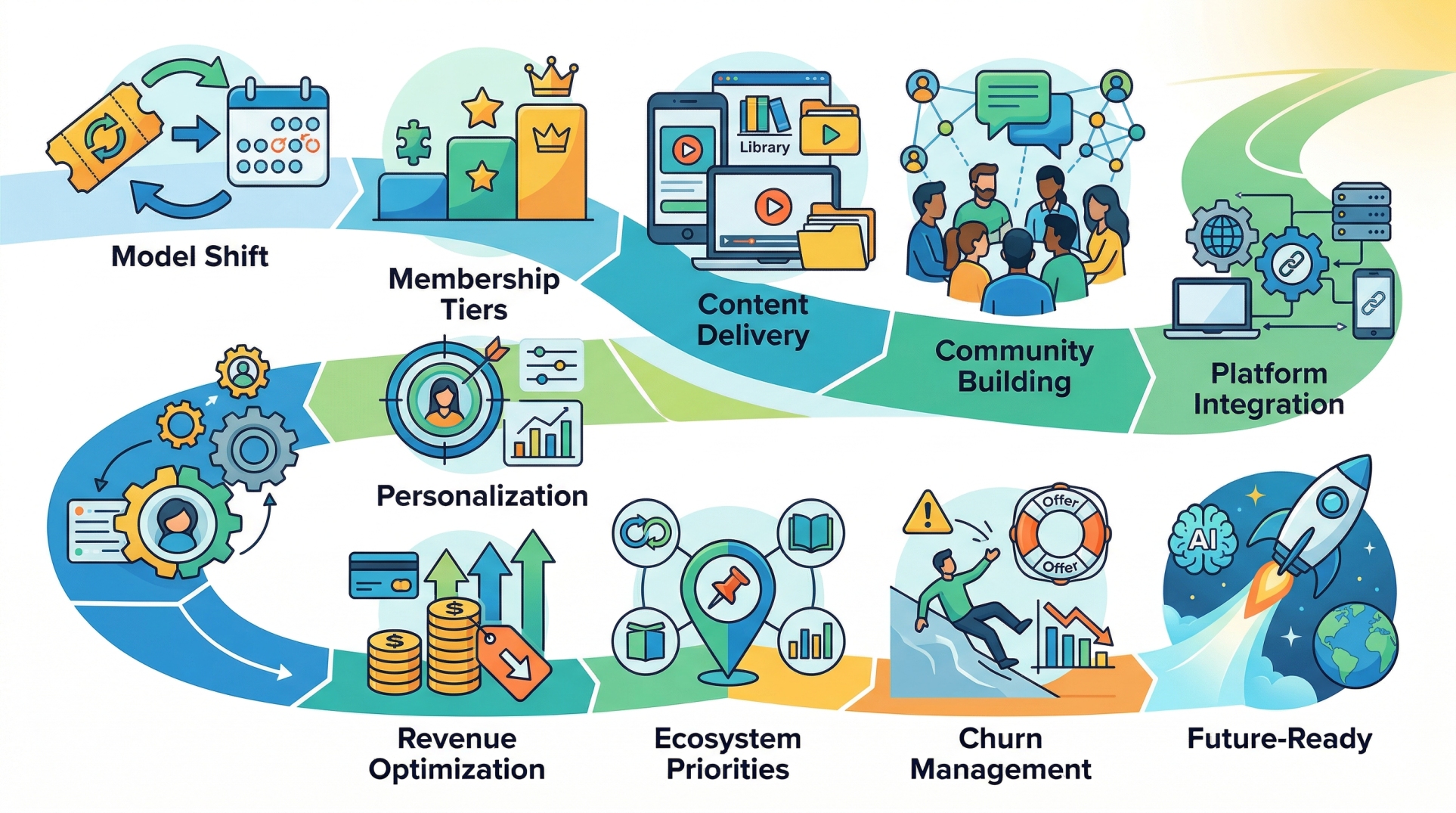
Step 10: Building a Future-Ready Verification System 🚀
• Adopt AI and machine learning for smarter verification 🤖
• Enable contactless and touch-free authentication methods 📲
• Continuously improve based on event data and feedback 📊
• Scale systems for large and global events 🌍
• Future-proof identity systems with modular architecture 🧩
Conclusion
Secure identity verification is a cornerstone of modern event technology. By combining advanced authentication methods, real-time monitoring, and strong data protection practices, event organizers can ensure both safety and seamless attendee experiences. As events continue to grow in scale and complexity, investing in robust identity verification systems will be essential for building trust, preventing risks, and delivering high-quality event experiences.
See more blogs
You can all the articles below
Ready to Find Your Perfect Solution?
Let us show you how Event Software can transform your events